Introduction
Cyber threats are no longer isolated incidents — they’re a daily reality for every organization operating in the digital world. From phishing and ransomware to data breaches and insider threats, the need for a structured approach to security has never been greater. That’s where cybersecurity management comes in.
It’s not just about installing antivirus software or firewalls. It’s about strategically managing risks, resources, and people to protect your organization’s digital assets from growing threats.
What Is Cybersecurity Management?
Cybersecurity management refers to the strategic process of safeguarding an organization’s information systems, data, and digital assets. It involves planning, implementing, and monitoring cybersecurity measures across technologies, processes, and people.
A strong cybersecurity management system ensures that your organization can identify, prevent, detect, and respond to cyber threats effectively — minimizing damage and maintaining business continuity.
In short, cybersecurity management is the backbone of a secure digital organization.
Why Cybersecurity Management Matters
Without a robust cybersecurity management strategy, organizations face higher risks of data breaches, identity theft, financial loss, and reputational damage. Cybersecurity isn’t just a technical issue anymore — it’s a business priority.
It helps protect:
- Personally Identifiable Information (PII)
- Protected Health Information (PHI)
- Financial and intellectual property data
- Mission-critical IT systems and infrastructure
A well-structured cybersecurity management plan allows companies to anticipate threats, manage vulnerabilities, and respond quickly when incidents occur.
Frameworks for Cybersecurity Management
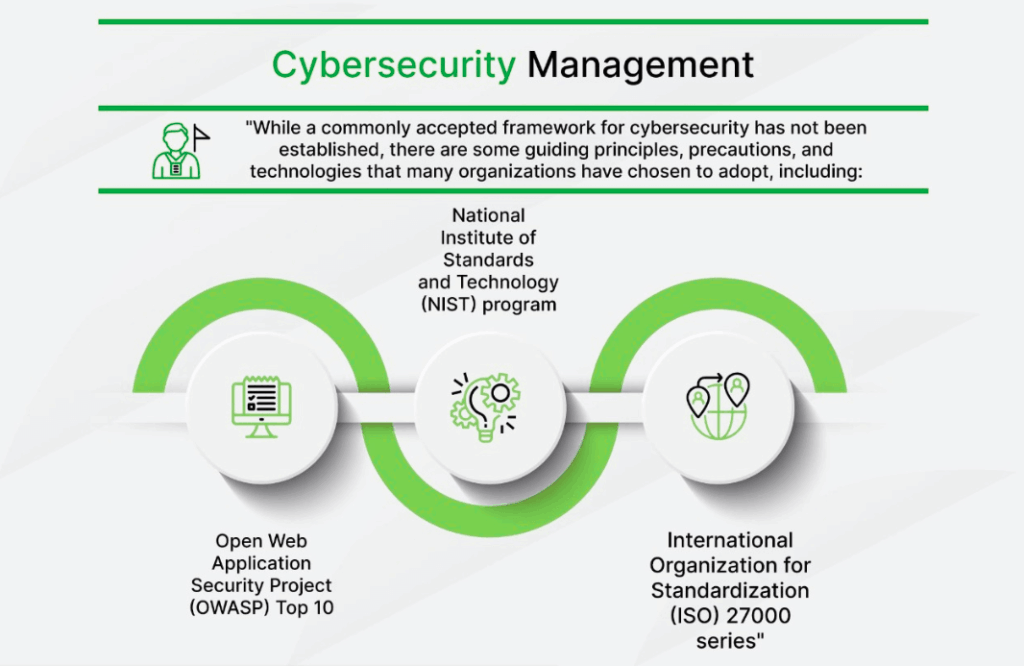
While there isn’t one universal framework, several globally recognized standards guide organizations in building strong cybersecurity management programs. Some of the most effective include:
- NIST Cybersecurity Framework (National Institute of Standards and Technology)
Provides a flexible approach to identify, protect, detect, respond, and recover from cybersecurity threats. - ISO/IEC 27000 Series
A family of standards for managing information security risk through policies, procedures, and controls. - OWASP Top 10
Focuses on identifying the most critical web application security risks.
These frameworks act as blueprints for companies to assess risk, prioritize investments, and maintain compliance with global standards.
Benefits of Cybersecurity Management
Implementing an effective cybersecurity management program helps organizations:
- Build a resilient enterprise security architecture
- Detect and mitigate advanced threats before damage occurs
- Secure IoT devices and remote access points
- Manage identity and access controls efficiently
- Gain real-time visibility into network vulnerabilities
It’s not just about defense — it’s about building a proactive, risk-aware security culture.
Cybersecurity vs. Cybersecurity Management
While both terms sound similar, they focus on different layers of protection.
- Cybersecurity is the technical aspect — protecting systems, networks, and data through firewalls, encryption, and security tools.
- Cybersecurity Management focuses on strategy — coordinating people, processes, and technologies to manage risks systematically.
In essence, cybersecurity is the “what”, and cybersecurity management is the “how.”
6 Best Practices for Effective Cybersecurity Management
1. Know Your IT Environment
Map all your digital assets — data, devices, cloud services, and endpoints. You can’t protect what you don’t know exists.
2. Create a Strong Risk Management Strategy
Assess your organization’s risk tolerance, identify vulnerabilities, and develop response plans that involve all key stakeholders.
3. Build a Security-First Culture
Cybersecurity awareness should be part of everyday operations. Regular training and communication make employees your first line of defense.
4. Use Continuous Risk Assessments
Cyber risks evolve constantly. Regular audits, threat intelligence, and adaptive risk management help you stay ahead of new threats.
5. Enforce Strict Security Protocols
Implement multi-factor authentication, endpoint protection, and encryption. Regularly patch systems and secure all remote access points.
6. Enhance Network Visibility
Use monitoring tools and real-time analytics to detect anomalies early. Transparency across your network reduces the time to respond to potential breaches.
Key Cybersecurity Risk Management Trends
1. Digital Supply Chain Risks
Attackers increasingly target suppliers and third parties with weak security to gain indirect access to larger networks. Strengthening vendor risk assessments is now essential.
2. Expanding Attack Surface
With IoT devices, remote work, and cloud environments, the number of potential attack entry points has skyrocketed. Managing this complexity requires automation and continuous monitoring.
3. Shared Cybersecurity Responsibilities
Cybersecurity is no longer the job of one team. Modern organizations are adopting a distributed security model, where every department plays a role in defense and incident response.
Final Thoughts
Cybersecurity management is no longer optional — it’s a core business function. As threats become more sophisticated and widespread, organizations must balance technology, governance, and human awareness to stay secure.
Whether you follow NIST, ISO 27001, or OWASP principles, the goal remains the same: protect your digital assets, manage risk effectively, and build a security-aware culture that can adapt to whatever comes next.
FAQs
Q: What is cybersecurity management?
A: It’s the strategic approach to protecting an organization’s digital infrastructure by managing people, processes, and technologies against cyber threats.
Q: What are the benefits of cybersecurity management?
A: It enhances risk visibility, protects sensitive data, supports compliance, and strengthens organizational resilience against cyberattacks.


