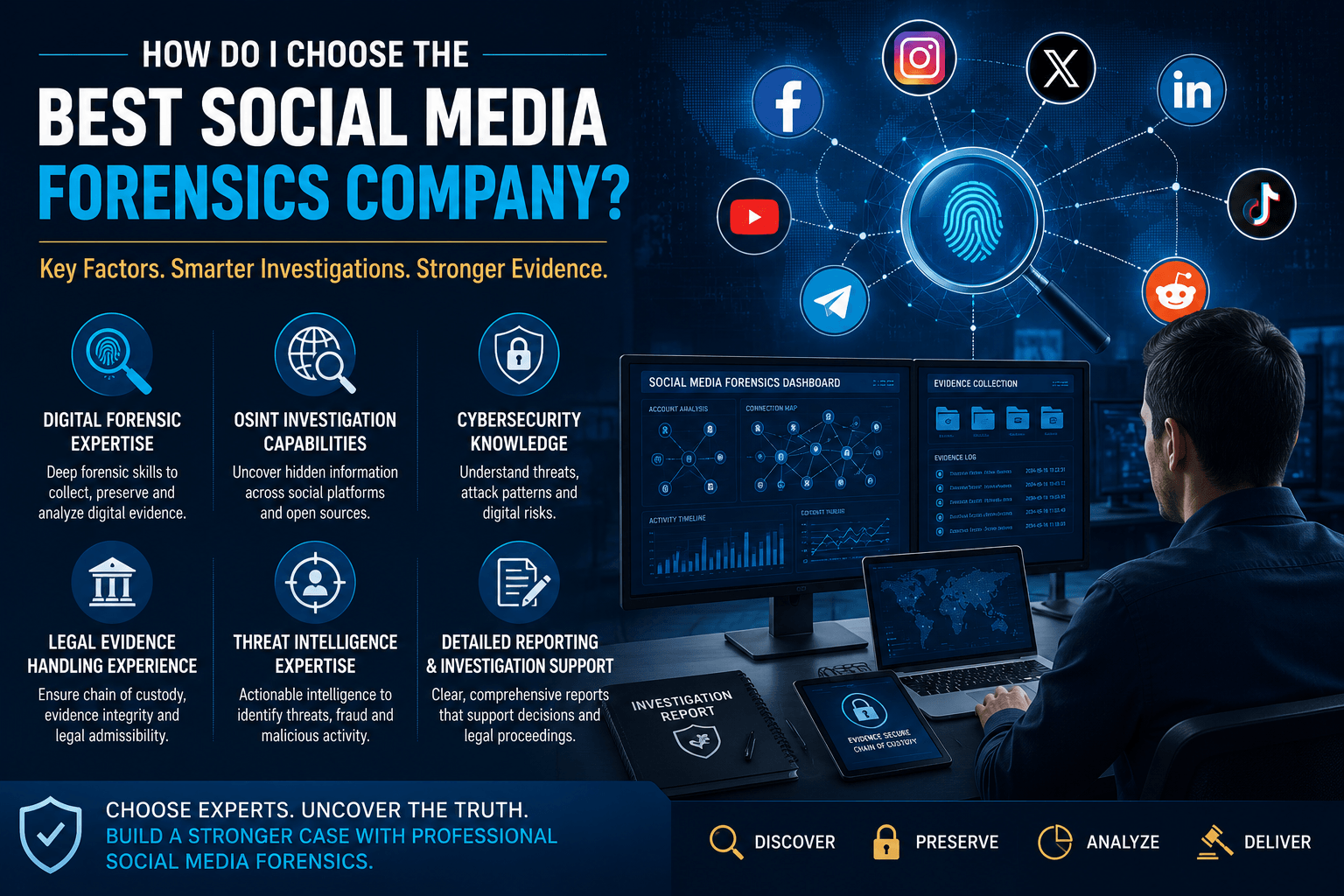
How Do I Choose the Best Social Media Forensics Company?
Social media platforms have become one of the most important sources of digital evidence in modern investigations. Whether the concern involves cybercrime, online harassment, fraud, insider threats, brand impersonation, intellectual property theft, employee misconduct, or legal disputes, valuable evidence often exists across platforms such as Facebook, Instagram, LinkedIn, X (formerly Twitter), TikTok, Telegram, Reddit, YouTube, […]