A Game Changer in Vulnerability Hunting: Introducing Vulnhuntr
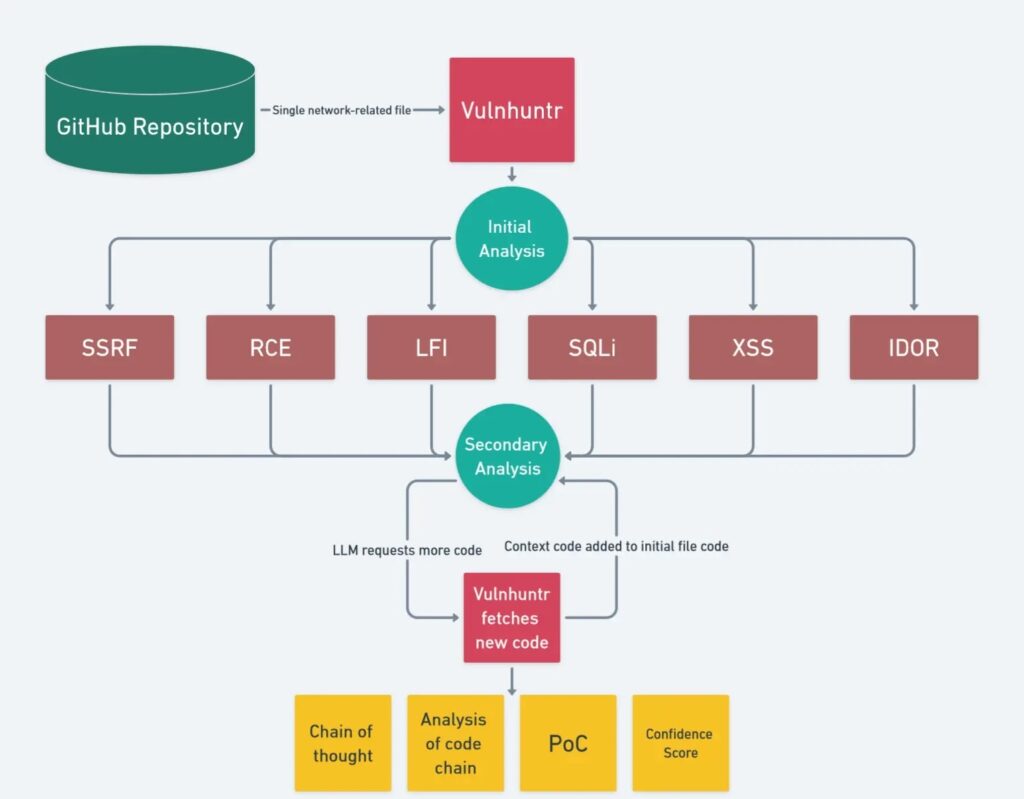
A new AI tool called Vulnhuntr has been introduced, reshaping the landscape of vulnerability discovery in open-source projects. Developed by Protect AI, Vulnhuntr leverages the capabilities of large language models (LLMs) to identify and explain complex, multi-step vulnerabilities, including remotely exploitable 0-day vulnerabilities, with remarkable precision and speed.
This tool has already demonstrated its prowess by uncovering critical vulnerabilities in high-profile projects with more than 10,000 GitHub stars.
Vulnhuntr to Detect 0-Days
In mere hours, Vulnhuntr identified over a dozen 0-day vulnerabilities, including Remote Code Execution (RCE) vulnerabilities in notable projects like gpt_academic, ComfyUI, FastChat, and Ragflow. What sets Vulnhuntr apart is its approach of breaking down code into smaller, manageable chunks rather than overwhelming the LLM with entire files.
This technique allows the AI to efficiently target specific areas in the codebase, drastically reducing false positives and negatives.
By repeatedly analyzing and reanalyzing code in a continuous loop, Vulnhuntr creates a detailed map from user input to server output. This process enables it to deliver comprehensive analyses, including proof-of-concept exploits and confidence ratings for each vulnerability detected. The tool prioritizes high-risk vulnerabilities, focusing on issues like:
- Local File Inclusion (LFI)
- Authentication/Authorization Flaws (AFO)
- Remote Code Execution (RCE)
- Cross-Site Scripting (XSS)
- SQL Injection (SQLi)
- Server-Side Request Forgery (SSRF)
- Insecure Direct Object References (IDOR)
Advanced Prompt Engineering Behind Vulnhuntr
Vulnhuntr utilizes advanced prompt engineering techniques to guide the LLM in finding vulnerabilities. These include:
- Best Practices Prompt Engineering
- XML-Based Prompts
- Chain of Thought Prompting
- Prefilled Responses
This structured approach ensures that the LLM performs thorough, logical steps to generate detailed reports on potential vulnerabilities. By narrowing down complex codebases to a few critical functions, Vulnhuntr significantly improves efficiency for bug hunters.
A Breakthrough in Static Code Analysis
While Vulnhuntr is currently limited to Python and focuses solely on remotely exploitable vulnerabilities, it is a considerable advancement over traditional static code analyzers. Its ability to map the entire call chain from user input to server output allows for more precise detection, reducing the risks of false positives and negatives.
As LLM technology evolves, expanding context windows to millions of tokens will further enhance tools like Vulnhuntr. Despite potential future advancements, Vulnhuntr’s hybrid approach of combining AI with static analysis ensures a higher accuracy rate in vulnerability detection.
Future Prospects for Vulnhuntr
Though Vulnhuntr is currently limited to Python, its underlying technology shows immense promise. As LLMs evolve and gain the ability to handle larger codebases and different programming languages, the potential for Vulnhuntr to revolutionize the vulnerability discovery process is vast. Its current limitations are merely stepping stones toward a future where static code analysis becomes less dependent on manual efforts, yet more powerful and scalable.
How to Get Started with Vulnhuntr
You can download Vulnhuntr from GitHub, or explore its capabilities as part of the AI bug bounty program at https://huntr.com. This platform incentivizes users to secure the growing open-source AI ecosystem, offering rewards for vulnerability discoveries.
For basic use, run:
bashCopy codevulnhuntr.py -r /path/to/target/repo
To target specific files:
bashCopy codevulnhuntr.py -r /path/to/target/repo -a subfolder/file.py
Key Features of Vulnhuntr:
- Advanced Prompt Engineering: Utilizes innovative techniques to guide the LLM through detailed steps in vulnerability discovery.
- LLM-Powered Call Chain Search: Maps the user input to server output for complete vulnerability paths.
- Python Static Analysis: Analyzes Python code to minimize false positives and negatives.
- Focus on High-Impact Vulnerabilities: Prioritizes remotely exploitable vulnerabilities such as RCE, XSS, SQLi, and more.
Final Thoughts
As the open-source AI ecosystem grows, Vulnhuntr stands at the forefront of securing it. By combining the power of LLMs with advanced static code analysis, it offers a powerful solution for detecting and explaining the most complex vulnerabilities. Tools like Vulnhuntr will be essential in the ongoing fight to secure open-source projects, ensuring that critical software remains safe from exploitation.
The future of vulnerability hunting has arrived, and it’s powered by AI.


